Capital is the lifeblood of business. Without capital, you cannot continue to fund your daily operations. Raising money for a business is just the first step to get it off the ground. Beyond that, you’ll need to raise funds to keep it moving.
According to the U.S. Bureau of Labor Statistics, lack of capital is one of the leading reasons businesses fail to survive, with just 25 percent of businesses lasting past 15 years.
Raising capital for your new venture is the initial order of business, so let’s dive into what it means and how to do it.
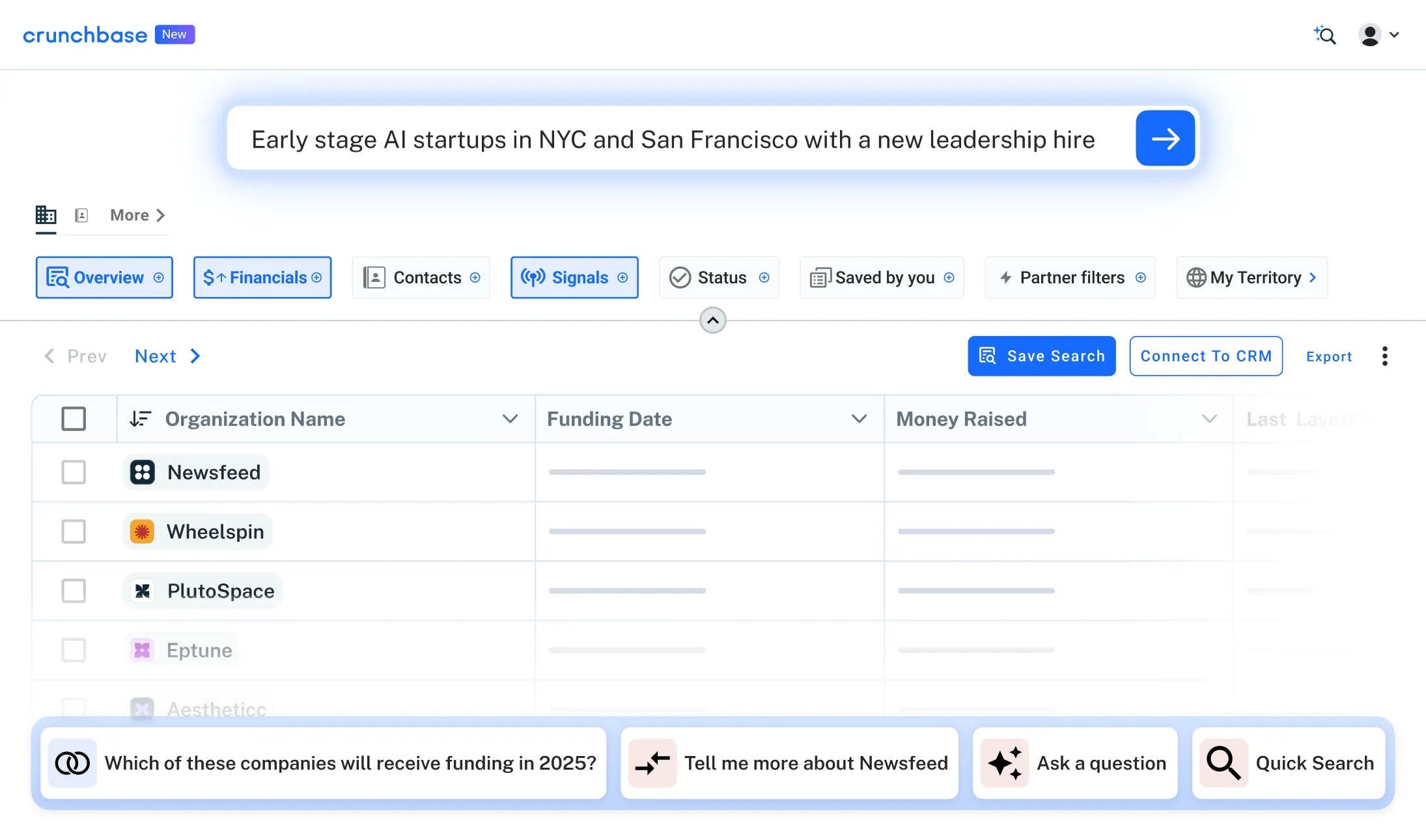
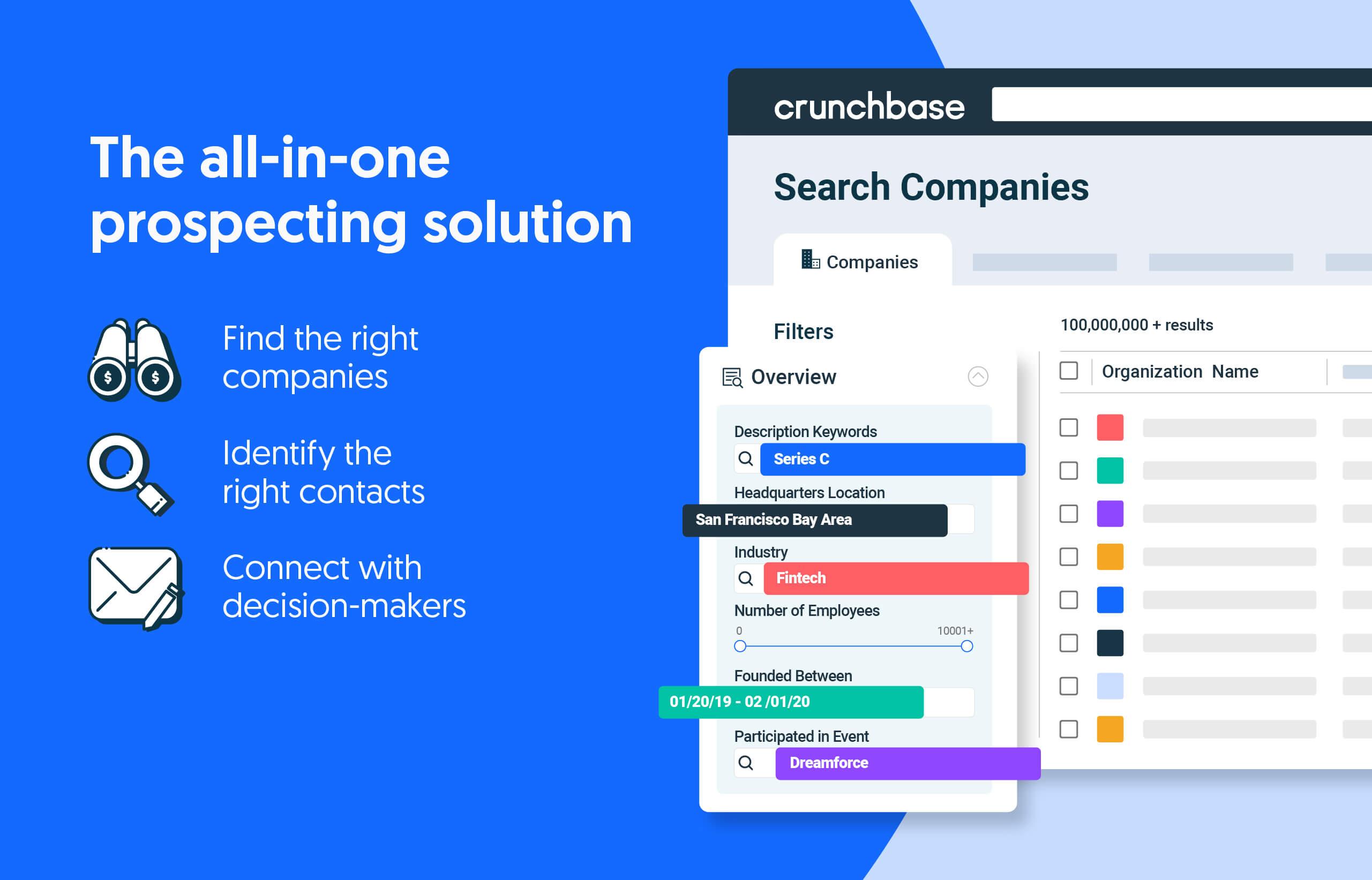
Search less. Close more.
Grow your revenue with all-in-one prospecting solutions powered by the leader in private-company data.
What is capital?
Capital is technically anything that can be quantified with a dollar figure within a business setup. A factory’s machinery counts as capital. Intellectual property could also be classified as a type of capital.
However, most people use the capital for business in terms of the money they have in the bank. Financial capital is often the difference between success and failure, so let’s talk about how to go about raising funds.
Types of capital for business
Raising capital begins with understanding your options for injecting that vital liquidity into your business.
Capital raising can come from a variety of sources. The right option for your company largely depends on your current circumstances and weighing the pros and cons of each option. Here are a few different types of capital.
Debt capital
Debt capital is the most common way startups get the money together to launch their businesses. The concept of debt capital is that you borrow money to raise the necessary funds.
Traditional bank loans, credit cards, online lenders and Federal loan programs are just some of the ways you can start raising capital via debt.
The average small business needs $10,000 to get started, but it depends on your industry and how ambitious you happen to be. Existing businesses will need to ensure they have a positive credit history to secure loans. In contrast, new business owners may use their personal credit scores to secure a loan.
The way debt capital is used depends on the size of the business. Although a small business may use debt capital by taking out a loan, corporations often choose to issue bonds, especially if national interest rates are low.
If looking at capital for business by taking out debt, watch your debt-to-income ratio to ensure you aren’t drowning in debt.
Pros
- It doesn’t dilute your ownership
- No lender claims on future profits
- Interest is tax-deductible
Cons
- Potentially higher interest rates
- May make it difficult to secure third-party equity investment
Equity capital
Equity capital comes in two forms: private and public equity capital.
Private and public equity capital comes in the form of shares in the company. The distinction is that a publicly traded company can be bought on the open market by anyone, whereas private equity is strictly traded among a closed group of investors.
When someone purchases a share in your company, they’re providing capital in the form of ownership. How much each share is worth depends on how many total shares you’ve got.
For example, if you have 100 shares and sell one share, each share is worth 1 percent of your company. Stock splits also allow you to create more shares to sell while diluting everyone’s ownership in the company.
It’s how small and growing companies can make a big splash.
Pros
- No repayment requirements
- Lower risk
- Bring in partners with expertise and talent
Cons
- You no longer own 100 percent of your company
- Time and effort required to secure equity investors
Net earnings capital
The final way to raise the funds is by increasing your net earnings. In other words, rather than giving away part of your company or taking on debt, you’re working to improve your output and profitability.
Net earnings capital is harder to come by because it’s typically powered by raising money in other ways to up your capacity and increase your reach.
However, if you’ve already got money from investors and are looking to expand even further, net earnings capital is a great way to drive your business forward.
Pros
- No lost ownership
- No debt
- Powered by genuine company growth
Cons
- Difficult to come by
- Higher taxes
How to raise money for a business
How do you go about raising capital if you are going into business for yourself? A complete understanding of capital raising is crucial to getting the funding needed to launch your new venture.
Determine your capital need
Before you can determine capital need, you’ll need to develop a long-term business plan and your company’s strategic goals. If you’re already operating, you have a leg up in understanding what it costs to run your business. If you’re just starting out, some of the expenses you need to take into account include:
- Office space
- Hiring new employees
- Purchasing technology/other hardware and software tools
- Marketing budget
You must strike a balance between having enough capital and not taking out too much capital. A lack of capital could indicate a broader weakness in your plan and the wider market. On the other hand, too much capital and you may find yourself giving away more equity than you intended or facing high monthly debt repayments.
Choose a funding type
You’ll almost certainly be choosing between equity capital and debt capital. When approaching venture capitalists, you will most likely need to give away a portion of the company, as well as a degree of control over business decisions.
With non-institutional investors, you’ll be taking on debt. Match up the potential debt repayments with your projected monthly revenue.
What works for one business may not work for another, so make sure you carefully think through your funding type.
Business valuation
The fundraising process begins with determining a rough value for the company. The entrepreneur needs to estimate how much their company is worth based on its potential. Equally, your assumptions need to be rational.
When seeking private equity or venture capital fundraising, you’ll need a pre-money and post-money valuation of the business. These estimates will determine how much of your company you’ll be giving away to investors.
Your post-money business valuation is the pre-money valuation plus any new money. Investors will ask probing questions regarding how you came to your pre-money valuation, so make sure you can show your rationale.
Connect with investors
It’s time to begin pitching your idea to investors. Keep this as condensed as possible because the more time you spend meeting with investors, the less time you have to manage the day-to-day operations of your business.
The easiest way to seek out investors is to leverage your professional network. Getting introductions in this way can be a launchpad for connecting with other interested parties.
The investor will present you with a term sheet if you receive an offer. This short document covers the primary points of the deal, such as how much is being invested, the amount of equity given in return, and any other high-level conditions.
You’ll have the opportunity to negotiate, but negotiation becomes significantly harder the moment you sign the term sheet.
Following funding rounds
Most successful companies don’t have just a single round of funding. A single round of funding may just be the jumping-off point for approaching more prominent investors.
Before embarking on your subsequent funding rounds, your pre-money value should be higher than the post-money value of the last round of funding. Why does this matter? New investors want to see that you’ve put your capital to good use and that this is a growing business.
Throughout each round of funding, you should be looking to fund anywhere from 12 to 18 months of operations before moving on to the next round.
Later rounds are traditionally more challenging to secure funding because investors who buy-in at later stages want to see proven business growth and momentum.
What’s the key to securing investment?
What investors want is simple: a positive (ideally outsized) return on their investment. Some may expect this return quickly, while others may be willing to stick it out for long-term growth.
Focus on the hard numbers and demonstrate that you’ve carried out meticulous research into your target market and the competition. Give accurate projections without exaggerating for effect. Experienced investors are well aware of business valuations, and being too ambitious could curtail your chance to raise money.
Condense your pitch and focus on the hard numbers that demonstrate to investors that they’re highly likely to see a positive return on their money.
9 things to know about raising capital
Figuring out how to raise funds can be intimidating the first time. There’s an art and a science to successful fundraising and a little bit of luck.
Follow these tips to increase your chances of securing the funding your new venture requires.
1. Get your material ready for investors
Focus not on what appeals to you but on what appeals to investors. All venture capitalists have a way they like to see businesses presented. Generally, your documentation should be well-structured and in an easy-to-read format.
Never tell an investor to visit your website to check you out. Investors are busy people and don’t have time to look you up themselves.
Give them everything they need right in front of them during your initial round of fundraising.
2. Create a strong business plan
The most important part of your pitch is your business plan. It should be a complete roadmap to success and a blueprint for how your organization will make money.
Investors don’t just want to see the financial figures. They want to know how you intend on operating your business, your marketing studies, as well as risk management, investment offering, and even an exit strategy.
Think like a chess player. Show that you’ve thought four moves ahead and planned for every eventuality.
3. Be clear on your competitive edge
What makes your business special?
No equity investor is interested in investing in one of a thousand other businesses. They’re searching for the movers and shakers that are about to change the game. If you’re just starting an accountancy business, no venture capitalist will show any interest because it’s nothing special.
Equity capital is different because investors want a piece of the next big revolution within your industry.
4. Concentrate on investors with niche experience
Some investors will indeed have fingers in many industry pies, but investors often come with more than money. Experienced business owners provide expertise to younger entrepreneurs. Talent and expertise come with the package because you’re not just getting capital. You’re getting a new owner.
Look for investors with experience within your niche. If you’re also providing them with influence over business decisions, you need the confidence that they know what they’re doing.
You should be looking to bring on investors only in a nonexecutive role if they don’t.
5. Talk about your management team
Remember, investors don’t know who you are. They don’t know if you’re a great entrepreneur in the making or a kid with an inheritance from mommy and daddy. You need to show that you’ve got the chops to make it.
Venture capitalists pay massive attention to the management team running the company. They want to know about their experience and personalities. There’s a reason many investors admit they give money to the entrepreneur rather than the business idea itself.
Don’t underestimate the value of your human capital because even the best business idea in the world won’t get far if the management team doesn’t meet the appropriate standard.
6. Know what the investor brings to the table
Inexperienced entrepreneurs tend to make the mistake of assuming that an investor is just someone who’s going to give them money. Investors form a valuable part of where your business can go.
Some investors can help you scale by having connections in emerging markets. If you’re looking to expand your business into Europe, India or China in the future, it makes sense to look for an investor with these types of connections. Investors may also sit on your board, playing a huge part in critical business decisions and the direction of your company, so ensure you’re aligned with the investor’s long-term vision for your company.
As already mentioned, an investor with technical expertise in your industry can also be helpful. Not every investor is hands-off, so make sure you question what they can bring to your emerging company.
7. Get your valuation independently certified
Where does one start when it comes to certifying a business? Unless you’ve had specific training or experience, the chances are you don’t know how to value your business.
Some entrepreneurs will pluck a figure out of thin air and run with it using a convoluted explanation. That’s not good enough for raising capital. Any investor with a degree of experience will see right through it.
Show your professionalism and credibility by enlisting the help of a professional valuator who can comb through your business plan and provide a realistic valuation.
Do this as early as possible so you know how much capital to ask for and which investors to approach.
8. Pitch with two essential documents
There are two critical documents you need when securing funding for your company. They are:
- Investor Pitch Deck: These presentations are roughly 10 pages/slides in length. It’s your first impression, so make it count. Investors scan through your pitch deck and decide whether they want to look at your formal business plan.
- Business Plan: If an investor wants to see your business plan, they’ll ask for it. This document is where you get into the nuts and bolts of your company.
Maintain a copy of these documents at all times when looking for capital. If investors like what they see in these two documents, they will ask for a formal in-person meeting.
9. Be persistent
Remember that many investors won’t reply to you at all. It doesn’t mean there’s anything wrong with your pitch, venture capitalists are busy people and don’t have the time to reply to everybody.
As long as you’ve meticulously combed through your documentation, you’ll find the right investor match sooner or later. What’s important is patience and maintaining focus on the critical operations of your business.
Conclusion
Debt and equity capital are the two primary ways you’re going to get a significant injection of cash into your business. If you’re strategizing and researching how to find investors for a startup, be sure you can clearly articulate your business plan and support that plan with relevant market research before you reach out to investors.
Crunchbase enables you to conduct market research, find and connect with the right decision-makers all in one platform.
.svg)




.webp)
.webp)